
How to Improve Your IELTS Reading Score Online
These are the steps you need to take to improve your IELTS reading score at home.
Launch your cybersecurity career with Google's 6-month Coursera program. Gain essential skills and job-ready knowledge.
E-student.org is supported by our community of learners. When you visit links on our site, we may earn an affiliate commission.
4.6 / 5
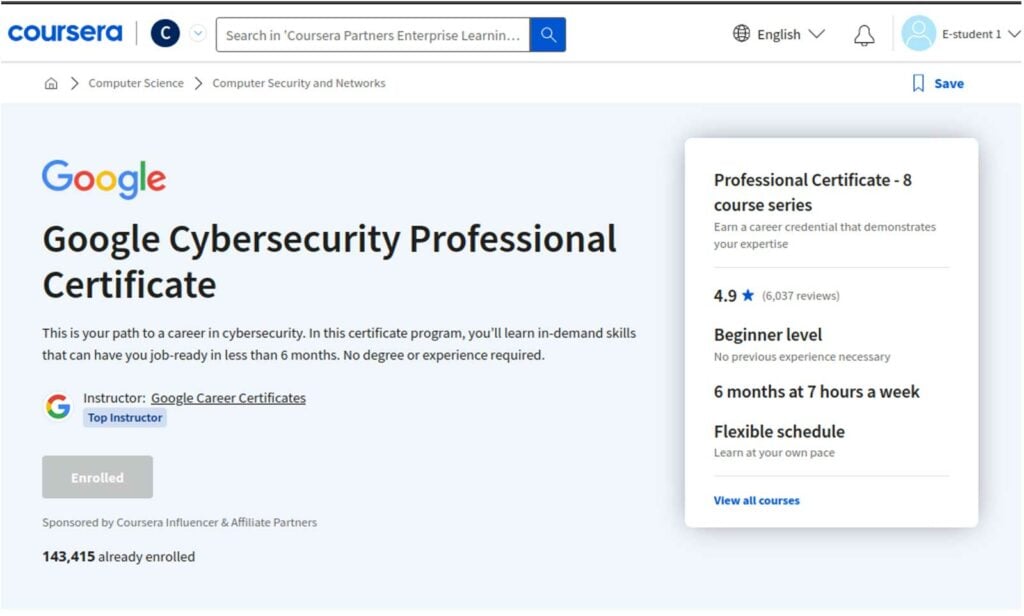
The Google Cybersecurity Professional Certificate on Coursera is a 6-month beginner-level program for anyone aspiring to build a career in cybersecurity, providing the necessary skills for an entry-level cybersecurity job. Introducing aspiring professionals to the fundamental concepts, the program also does a good job of providing an overview of some of the common tools you will interact with as a cybersecurity expert. Learners who dedicate the necessary attention to the course should get sufficiently skilled to be able to apply for a job – but we would still recommend most learners to complement the program with additional courses or portfolio work.
The work of a cybersecurity professional might not be like in Hollywood movies – most in the sector are not flying around the world trying to catch cybercriminals while bullets are flying around them. Despite that (or rather thanks to it!), cybersecurity should be at the top of any career counselor’s list of recommendations: it has zero unemployment, thousands and thousands of unfilled positions, exciting career development possibilities, and interesting and exciting work (albeit potentially somewhat stressful at times).
Part of the problem has been the lack of quality education to introduce new professionals to the field. Given this, the introduction of the Google Cybersecurity Professional Certificate program on Coursera – promising to get novices to a point where they can take on entry-level jobs – generated quite a lot of buzz. In this review, we’ll have a look at this program in more detail to see whether it lives up to its promise.
Assessments aren’t just standalone evaluations; there are also several seamlessly integrated assessments into the curriculum hence they ensure that you apply the acquired knowledge actively. Moreover, the courses have practical examples, tasks and lab activities that give you hands-on experience.
The Google Cybersecurity Professional Certificate program on Coursera requires the completion of 8 courses, taking an estimated six months at a study pace of 7 hours per week. For those who are planning to enroll, it operates on a subscription plan costing $49 per month, totaling $294 for the entire duration. You can, however, also complete the certificate in less than six months, which would result in paying less.
If you are a Coursera Plus subscriber, the Google Professional Certificate is included. While this is a bit more expensive at $59 per month (or $399 for a year), it gives you access to most of Coursera’s course catalog.
As for most Coursera courses, it is also possible to audit the individual courses of the Professional Certificate for free. Coursera also provides a 7-day free trial as well, which allows a review of the course material before committing to a paid plan.
Google Cybersecurity program’s structure reflects a practical approach to learning. With various modules strategically curated to instill fundamental knowledge, participants are equipped with skills that are both practical and relevant. Learners are able to get a solid understanding of cybersecurity concepts and also cultivate the ability to apply concepts learned effectively by using this approach. According to Coursera, 75% of those who took this course reported a career improvement.
As long as you are able to dedicate the needed time to this program, it can open up whole new career possibilities. Whether you are paying $300 or you manage to complete it faster and pay less, it is a very reasonable investment in your future.
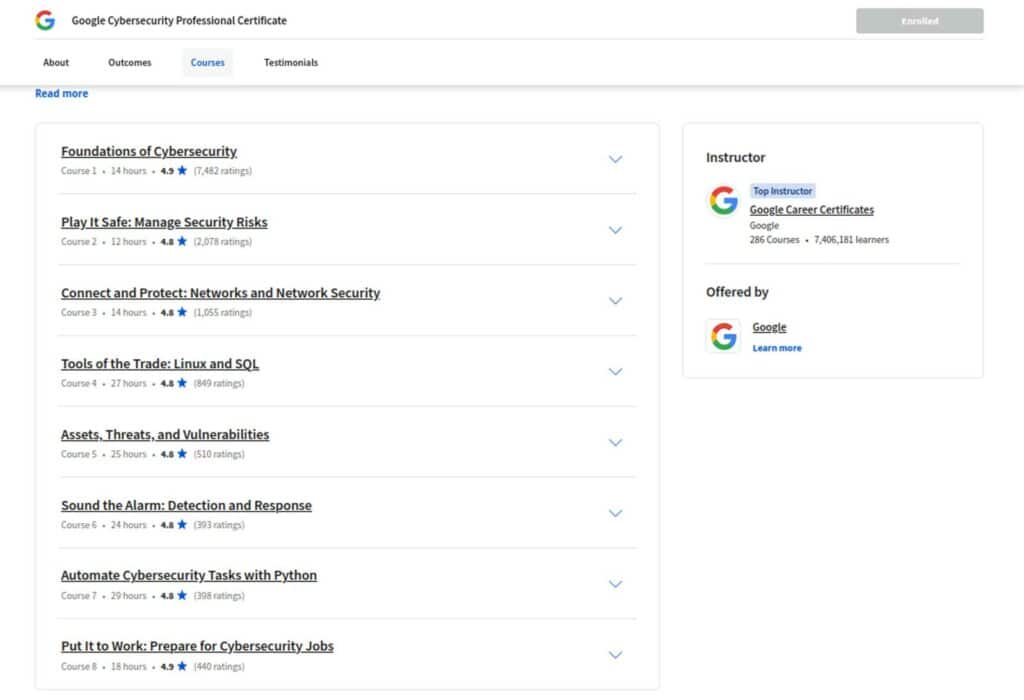
The complete Certificate program has 8 component courses:
To give you a better idea of the program, we’ll go through each of these courses in more detail below.
The first course, Foundations of Cybersecurity, gives a basic introduction to the different terms and tools learners will come across while undertaking the program. The instructors introduced the learners to different events that played a major role that led to the development of cybersecurity. Common security frameworks and controls used to mitigate organizational risks are discussed in this course. Learners are also introduced to programming languages and how each language is used in the cybersecurity field.
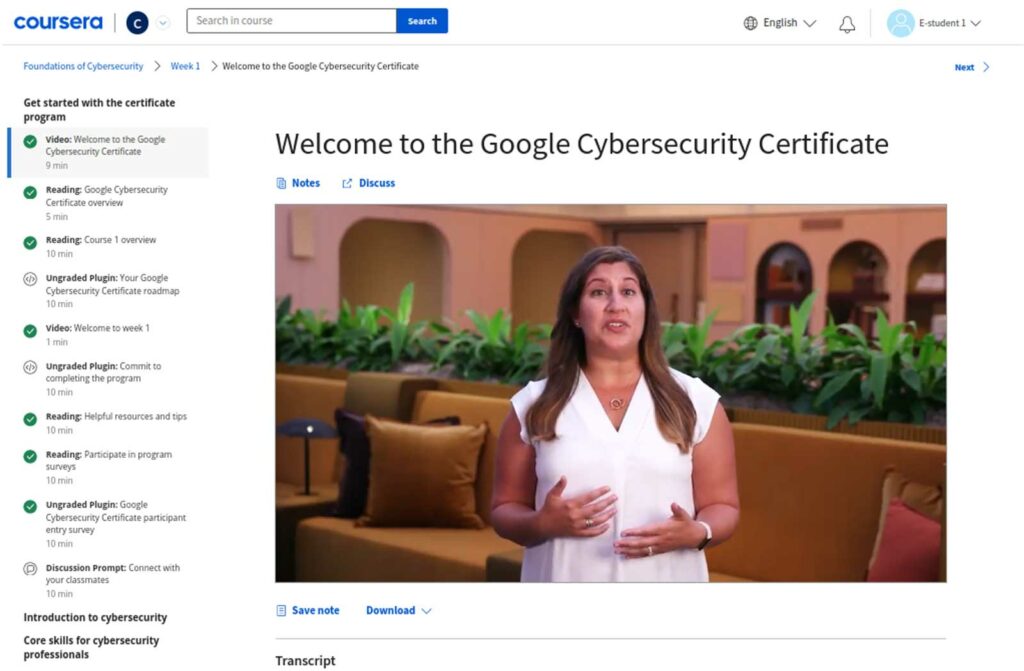
Learners are also given a first introduction to tools used to analyze network protocols and security information and event management tools (SIEM). Each module has quizzes that ensure the learners get a good grasp of what is taught. The course will take a learner about fourteen hours to complete.
This course starts by explaining to the learners the eight domains of cybersecurity. The learner is introduced to the different categories and types of vulnerabilities, risks, and threats. Week two introduces learners to security frameworks and controls and the three components of the CIA triad (confidentiality, integrity, and availability). Relationships between the various frameworks and controls are explained to help learners understand how they are used in real-world scenarios. Moreover, instructors introduce the Open Web Application Security Project (OWASP) security principles.
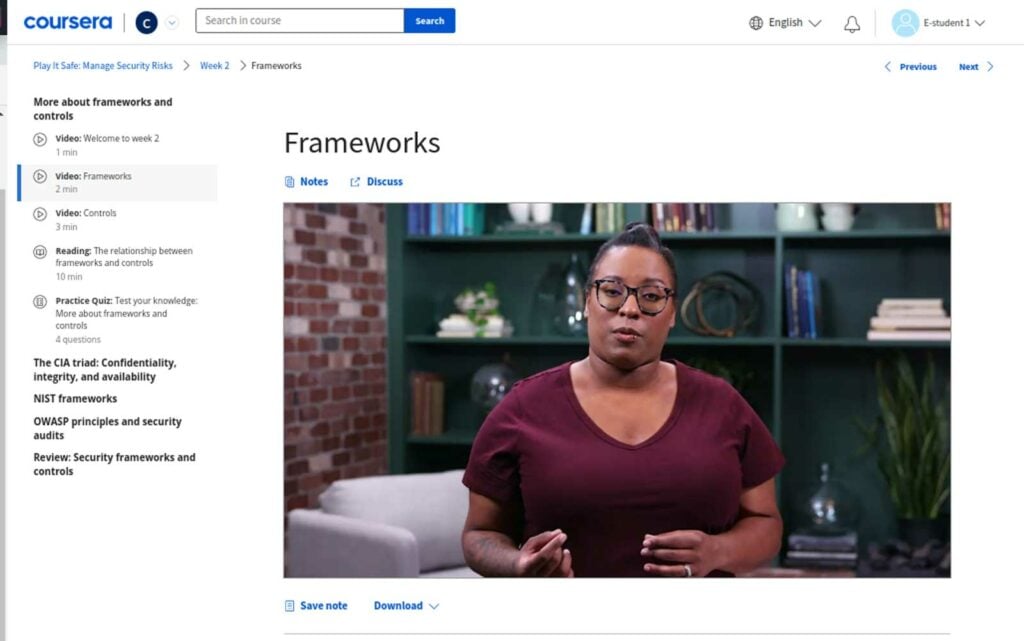
The NIST framework is extensively discussed, and some of its functions and use cases. The latest cybersecurity threats are explained in this course to equip learners with knowledge of what they will likely face in their jobs as cybersecurity professionals. Learners are taught some of the standard processes to follow while performing a security audit for an organization.
Instructors give the learners a glance into functions and some of the common security information and event management tools during the third week of this course. Learners are taught how the SIEM tools are used to protect organizations. The last module covers the instructions for utilizing playbooks. Learners are introduced to the application of playbooks within the realm of cybersecurity, where they learn how to use them to respond to identified threats, risks, and vulnerabilities.
The first module of this course introduces learners to network architecture followed by organization’s network security. Common security threats and vulnerabilities are discussed and the methods to remediate them. Chris, the instructor, talks to learners about his journey in the cybersecurity profession. He motivates the learners by explaining how the Google Cybersecurity program can be used as a stepping stone to launch a successful career in cybersecurity. Tina shares her experience of what it is like to work as an engineer as Emmanuel lists some of the useful skills for those aspiring to become network security engineers.
The network operations module introduces learners to the various network protocols and the vulnerabilities that may arise as a result of network communication. The 3 major categories of network protocols are explained in this module: communication protocols, management protocols, and security protocols. Antara, who is a security engineer at Google, gives learners a taste of life in her work. She explains some of the day-to-day tasks a security engineer performs at his/her job. She explains to learners about encryption algorithms and how they are used to secure network communication. Other important topics covered in this course include; firewalls, VPNs, the importance of proxy servers in ensuring network security, virtual networks and privacy and the different VPN protocols.
Other modules include security against intrusions, where the learners are introduced to different techniques to safeguard network systems and devices against common attacks. In the last week of this course, learners are taken through security hardening. Through system security hardening, a cybersecurity expert can protect systems against common intrusion methods and malicious actors. This course will take you about fourteen hours to finish.
In this course, the learner acquires an understanding of the various aspects related to Linux and SQL. The first module introduces the operating systems fundamentals, resource allocation and virtualization technology. With the guidance of the instructor, learners explore the graphical user interface and command-line interface comparing them to grasp their unique features and functionalities.

Learners are introduced to the Linux operating system, its architecture, and the different Linux distributions and learn how they can use the Linux shell to perform actions on the operating system.
During the third week of this course, learners are taught the various commands they can use in the bash shell. By finishing this module, learners can use the bash shell to navigate the file system, manage file content in bash, and authenticate and authorize users. The module has a section where they will learn how to get help while using Linux to get around some of the common problems users face. There are labs in this module to help learners grasp some commands that they will be using regularly as cybersecurity experts.
the last module in this course covers databases and Structured Query Language (SQL). Learners learn the difference between SQL filtering and Linux filtering. Crafting SQL queries is taught in this module. There are several lab activities in this module to ensure the learners grasp the concepts taught. This course will take you approximately twenty-seven hours to complete.
One of the major tasks of a cybersecurity practitioner is ensuring the safety of the organizational assets. In this module, learners begin by learning the different kinds of assets found in an organization and how the bad actors can exploit vulnerabilities within them to their advantage.
In this module, the instructor takes learners through identifying the various types of threats that an organization may be exposed to. The instructors guide learners on how to use NIST framework standards and guidelines learned earlier to manage cybersecurity risk.
After identifying threats to a system, the next step would be to protect them from the bad actors. In the second module, learners are taught the importance of privacy in asset security. Instructors expound on the important role played by encryption in maintaining the privacy of digital assets. The importance of hashing in ensuring the integrity of files and the different access control and authentication systems is taught too. Finally, learners are taught how to determine appropriate data handling practices, safeguarding information, encryption methods, and finally, a real use case activity where learners are supposed to improve the authentication, authorization, and accounting for a small business.
In the third module of the course, learners are taken through the vulnerability management process. Instructors take learners through some of the common vulnerabilities i.e., OWASP TOP 10 and how bad actors exploit these vulnerabilities. The last module introduces learners to the common types of threats to digital asset security. Instructors introduce the threat modelling process and teach ways in which professionals can prevent breaches from happening. This is a beginner-level course and it will take you approximately twenty-five hours to complete.
This is a beginner course that equips learners with knowledge which is important for those aspiring to become cybersecurity analysts. Learners are taken through the incident response life cycle. Fatima, a cybersecurity professional, explains to the learners the importance of communication during incident response. Incident response plans, tools, value of documentation and intrusion detection systems are discussed in the first module of this course.
The second module builds upon what was taught in Connect and Protect: Networks and Network Security course. Learners are taught network traffic and how to capture and view the captured network packets. Different ex-filtration attacks that the bad actors may use are explained. There are several labs where learners are encouraged to try out these principles in practice.
Instructors delve deeper to explain the various processes and procedures found in incident detection, investigation, analysis, and response stages. Instructors expound on why the logs are important and the different variations of logs. The course guides the learner on how to investigate suspicious file hash, verify and respond to incidents, use a playbook to respond to an incident, response and recovery, and finally review the final report.
In the last module, learners are taught about the role of Security Information Event Management (SIEM) systems and intrusion detection systems. You need to understand these tools well as you will come across them many times in your job as a cybersecurity expert. The course will take you about twenty-four hours to finish.
Learners are introduced to the Python programming language and its use cases in the field of cybersecurity. No prior programming knowledge is required to undertake this course since it is a beginner-level course. The first module introduces learners to Python fundamental concepts such as conditional statements, data types, iterative statements and variables.
Learners are introduced to both predefined and user-defined Python functions. Writing effective code is the main focus of the second module. With knowledge acquired in this module, learners can write readable, effective and reusable code. The course includes interactive labs, exercises and quizzes which ensure the concepts introduced are well understood.
Working with lists and strings is the third module of this course where the learner is introduced to various concepts, he/she will come about while working with lists and strings. As a cybersecurity professional, you will be working with strings and lists on many occasions, for example, when working with an organization’s device IDs it is more reasonable to store the IDs in a list since you can access all the IDs using a single variable.
Since this is a programming course, the last module is for practice. In this module, learners are guided on how they can automate cybersecurity-related tasks. instructors guide the learners to working with files using Python. By the end of this module, the learner can open and read files, parse files and the structure of their content, and finally to effectively debug code. The module involves exercises where learners practice what has been taught in each module. One exercise that stands out in this course is the last one, where the learner is required to debug code.
This is the last course in the Google Cybersecurity program. The course starts with providing links to the various discussion forums where learners can connect and share knowledge with other learners. Dion, a cybersecurity professional, gives a peek into his professional journey as a cybersecurity expert. Learners are taught how to classify different data and assets, protect assets and events and incident detection. Learners will gain knowledge on disaster recovery and business continuity, embracing their role in sensitive data handling and how to detect and protect without neglect.
In the second week of the course, learners are introduced to escalation in cybersecurity, when to escalate and not to escalate and the importance of timing to avoid causing much damage. Analysis of cybersecurity incidents and their impacts is also done in this course. Communication is key in the cybersecurity profession. Learners are taught how to communicate effectively to influence the stakeholders. The three main key concepts discussed under this module include; understanding your stakeholders, communicating for impact and visual communication using dashboards.
On the second last week of the program, learners are now ready to start a job as cybersecurity professionals. This module has resources to use to expand your knowledge in the cybersecurity field. Learners are encouraged to network with other cybersecurity experts who play a major role in helping learners navigate the profession without many challenges.
Learners are required to write a resume based on a template provided that they will use in their job search. They are taken through the process of developing an elevator pitch and on the various ways to prepare for interviews. This course takes about eighteen hours to finish.
The Google Cybersecurity Professional Certificate program provides beginners with an outstanding introduction to critical cybersecurity concepts. It presents the materials in a clear and easy-to-understand manner. Regardless of your level of knowledge, this course is designed to build a solid foundation. It covers a wide range of topics, from technical aspects to practical applications, including threats, vulnerabilities, and risk management strategies. The program delves into the historical events that have shaped this ever-evolving field. By understanding the roots of cybersecurity, learners gain a deeper appreciation for its significance in today’s digital landscape.
The course does an excellent job of highlighting the paramount importance of cybersecurity in the modern business world. It unravels the pivotal role cybersecurity plays in safeguarding sensitive data and ensuring the seamless operation of businesses in an increasingly digital society.
While the program is structured to deliver fundamental concepts and theoretical knowledge, there are some limitations. The course could benefit greatly from the addition of more practical exercises, especially in the realm of Security Information and Event Management (SIEM) tools, which are crucial in real-world cybersecurity roles. Another area that is largely missing concerns SQL vulnerability prevention, input validation, and SQL injection attacks, all of which can be considered fundamental topics.
In an age where cybersecurity is paramount, the Google Cybersecurity course stands out as an exceptional resource. It equips individuals with the knowledge and skills necessary to navigate the intricate landscape of cybersecurity while providing historical context and highlighting the significance of this field in our digital age. Whether you’re a beginner or have some prior experience, this course is a valuable stepping stone toward a rewarding career in cybersecurity.
In conclusion, the Google Cybersecurity Professional Certificate program is an excellent starting point for anyone looking to enter the cybersecurity field. It offers a well-structured curriculum, expert instructors, and the flexibility of self-paced learning. While it may lack some depth and hands-on practical exercises in certain areas, its accessibility and the knowledge it imparts make it an invaluable resource for beginners. Graduates of this program will have the confidence and skills necessary to pursue entry-level cybersecurity positions, making it a commendable initiative in the ever-evolving world of cybersecurity education.


These are the steps you need to take to improve your IELTS reading score at home.

Here’s how to sell & market online courses to make your online course business thrive!

These are the very best Coursera courses from the e-learning giant’s massive catalog of free courses.